Cloud Security Challenges: How to Ensure Print Security in The Cloud
Cloud Security Challenges
One of the key tenets of cloud computing is the reduction of hardware and software ownership and maintenance which allows organizations to focus on their core business strategies and strengths.
We are already seeing this trend with organizations consolidating remote print servers to centralized data centers in the form of serverless printing.
While the financial and operational benefits are obvious and similar, cloud computing goes one step further by eliminating the burden of infrastructure management altogether and enabling organizations to quickly align information technology to business strategies through on-demand provisioning.
However, by adopting a cloud service, organizations have to give up direct control of whatever system they are moving to the cloud which naturally spawns concerns over security.
This document will address common security concerns organizations have regarding moving their printing infrastructure to the cloud and how UniPrint Infinity ensures security in the cloud.
Some of the common Cloud security challenges include the following:
- Insecure interfaces
- Identity and credential management
- Account and traffic hijacking
- Data breaches
- Data loss
- Shared technology vulnerabilities
The above security concerns will be addressed for both UniPrint Infinity deployment in Microsoft Azure and UniPrint Cloud.
Insecure Interfaces
Generally, APIs and UIs are the most exposed part of any cloud application system. Hence, adequate controls protecting them from the Internet are the first line of defense.
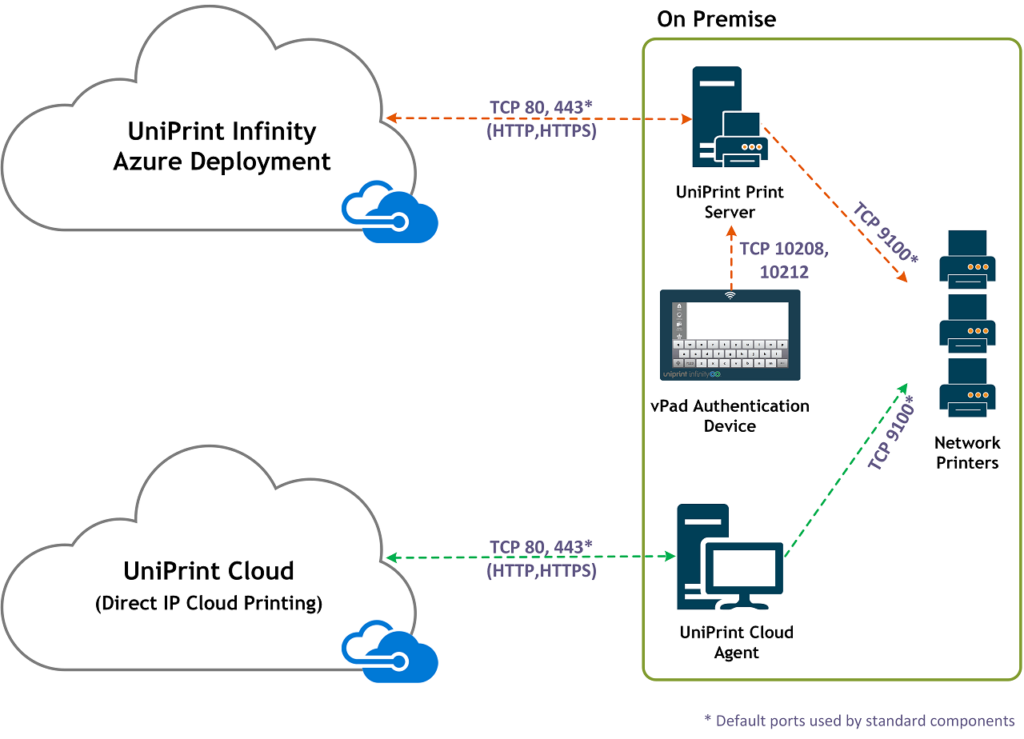
Since UniPrint Infinity Azure Deployment and UniPrint Cloud employ Microsoft Azure Active Directory (AD) and SQL, logging into UniPrint Infinity or UniPrint Cloud from an external IP address is all managed by Azure.
Identity and Credential Management
Incidences such as data breaches can occur because of insufficient identity and credential management. Failure to use multifactor authentication and using weak passwords are usually the culprit.
UniPrint Infinity Azure Deployment and UniPrint Cloud leverages Azure Active Directory identity and access management.
For UniPrint Infinity Azure deployment an on-premise directory can be integrated with Azure AD for a hybrid identity management solution.
Account and Traffic Hijacking
The easiest way to hijack accounts and traffic is by obtaining user credentials and traffic eavesdropping.
With stolen credentials, attackers can access critical areas of a cloud computing system and compromise the confidentiality, integrity and availability of this system. This vulnerability is addressed using Azure AD and educating users on creating and using strong passwords.
To protect against hijacking, UniPrint Infinity utilizes Azure security which ensures all connections to the Azure SQL database are encrypted using (SSL/TLS) at all times while data is “in transit” to and from the database.
Data between the UniPrint Print Server and a vPad device uses RC4-64 bit. This lower encryption scheme is necessary in order to comply with US cryptography device export regulations.
A 256-bit encryption and optional architecture is also an available option to reduce any sniffing risk.
Interested in finding out more about how you can ensure complete security in the cloud? Check out this free whitepaper on secure cloud printing!
Data Breaches
A data breach is an incident whereby sensitive or confidential information is released, viewed or stolen by an unauthorized user. A breach may be the result of a primary attack or simply human error.
Data breaches are not unique to cloud computing and can even occur in traditional networks, however they seem to be one of the top concerns for most organizations probably due to shared resources in a third-party data centre.
The best and easiest measure to prevent a data breach is to properly manage user identity and access to sensitive information by enforcing multifactor authentication and using encryption. Microsoft Azure AD is used to address this.
For printing, however, another possible data breach is leaving sensitive documents on a shared printer. This obviously occurs after a user clicks Print, becomes distracted and then forgets that they printed something in the first place. The solution is to change how users print by making them more conscious of their printing habits.
This is where secure pull printing comes in. With secure pull printing, the user must enter a password at the printer or at an authentication device in order to release their print job to a printer for printing.
Since they are already at the printer, distraction is kept to a minimum and printed documents are collected right away.
By using UniPrint SecurePrint, multi-factor authentication can be used whereby the user is required to tap their RFID or HID card and also enter a SecurePrint password before their print job is released for printing.
Data Loss
Stored data in the cloud can be lost to due to reasons other than from a hacker attack. Data can be accidently deleted by an authorized employee or lost from a physical catastrophe such as an earthquake or fire.
Microsoft Azure offers many different ways to back up and store data, including an option to store data off-site at multiple locations.
Shared Technology Vulnerabilities
Since cloud computing uses multitenancy, systems and data from various organizations are placed in close proximity to each other. Since memory and resources are shared access to one tenants’ data can give way to access other tenants’ data.
Regular patch implementations can go a long way to preventing this, as well as employing strong compartmentalization such that individual tenants do not impact the operations of other tenants.
This is especially true for a SaaS implementation such as UniPrint Cloud. Since UniPrint Cloud runs in Microsoft Azure, Azure takes care of most of the isolation including Microsoft Azure SQL Database which employs database isolation measures to ensure that tenants only have access to their data and not any one else’s.
Ensuring Cloud Security
Cloud printing and cloud computing in general requires a multi-layer approach towards security in order to address various security concerns.
The responsibility of ensuring that printing is secure lies with both the vendor and the customer. The vendor is responsible for ensuring that the provided cloud infrastructure and the customer’s data are secure.
The customer is responsible for ensuring that access to their data is secure by enforcing user authentication and that physical access to the premise is secure.
With UniPrint Infinity and UniPrint Cloud being hosted in Microsoft Azure, Microsoft is responsible for the infrastructure, by ensuring their data center is secure and ensuring each customer’s data is isolated.
However, to ensure printing is truly secure the risk of data breaches from sensitive documents left on shared printers needs to be reduced.
UniPrint SecurePrint, along with the UniPrint vPad authentication device extends the security provided by Microsoft Azure, by ensuring sensitive documents are not left on shared printers.
Users are forced to print consciously and multifactor authentication is required in order to release their print jobs for printing. SecurePrint easily integrates with Active Directory and Imprivata OneSign.
For multifactor authentication, the UniPrint vPad comes with a built-in RFID or HID reader. External card readers are also available for purchase. Since the vPad is compatible with any printer make and model, standardizing an existing printer fleet is not necessary.
Whether an organization is moving their entire IT infrastructure to the cloud, or just their printing infrastructure, UniPrint Infinity has a secure printing solution that is easy to integrate with minimal configuration.
Try UniPrint InfinityCloud
Whether you are printing at the office or at home, UniPrint InfinityCloud is the cloud printing solution of choice for your organization.
Recent Posts
- Cloud Printing Management: The Secret to Fewer Help Desk Tickets
- Why Should You Outsource Printing Management? A Comprehensive Overview
- How Cloud Print Management Prevents Print Server Vulnerabilities
- Is Printing Dead?
- How InfinityCloud Outshines Microsoft Universal Print in 2024
- How the Cloud Print Management Software Drives Sustainable Business Practices
- How Cloud Print Management Enhances Your Network Security
- How to Enhance Remote Work Experience with Secure Serverless Printing
- Update to Google Drive Cloud Storage
- A Guide to Preventing Phishing Attacks
- See All