Secure Print: 5 Print Security Threats to Watch Out For
In the past, printers were simple machines where a user would print to one local printer and then go retrieve whatever document they printed.
There have always been security issues with legacy printers such as the theft of documentation from the printer before it can be collected. Unfortunately, innovation in software and technology has opened doors to a wide array of new print security threats enterprises must be aware of.
Network printers are often a serious data threat as these machines often handle sensitive information and could provide an access route to other computers on your network.
Additionally, advanced multi-function printers are subject to an even larger number of print security threats because they are essentially self-contained computers with their own hard drive, operating system, and direct network connection.
What is Secure Print?
The secure print mode is precisely a printing mode that is used when printing confidential documents. These can range from corporate documents to patient prescriptions, bank notes, cheques, and even identity cards.
Therefore, a printer requires a hard disk for secure printing and will not automatically print a document. For secure print, the user needs to enter a password, after which the print will be provided. As a result, only specific people will have access to secure print and in turn confidential documents.
5 Print Security Threats To Watch Out for
There are five main print security threats to watch out for:
Document theft or snooping
The most obvious threat to print security is individuals intentionally (or accidentally) picking up a confidential document at the printer tray which doesn’t belong to them.
This can be easily solved by implementing a secure pull printing solution for all users. Using this solution, printed documents are only released when users authenticate themselves by password or swipe card physically located near the printer.
Using this strategy, confidential documents are only released on-demand to the user who is intended to see them.
Unauthorized changes to settings
If your printer settings or controls are not secure, a hacker can easily manipulate printer settings, erase critical data stored on the printer, view saved copies of previously printed documents, or even erase all of your settings.
It is crucial for all printer control panels to be password-protected, preventing hackers from changing settings or accessing sensitive data without your knowledge.
Every system administrator should know the basics of implementing a password and encryption security plan to avoid unauthorized access to printers.
Saved copies on the internal storage
Are you planning to throw out old legacy printers? Be very careful.
Firstly, always check if the printer has an internal drive. If it does, ensure it is fully wiped to avoid data scavengers digging through them to find sensitive information as soon as the printers hit the junkyard.
Although unlikely, a disgruntled employee or someone at the office can also easily steal the stored information physically either by unplugging it and walking out or by transferring files onto another drive directly.
No matter the scenario, special attention must be placed on printers with internal storage units to ensure the information contained does not leave where it is meant to be and that is in the office.
There are special drive wiping programs that make the data completely unrecoverable.
Interested in learning more about how you can achieve a secure print infrastructure? Check out this free whitepaper on achieving a secure print infrastructure!
Sniffing network printer traffic
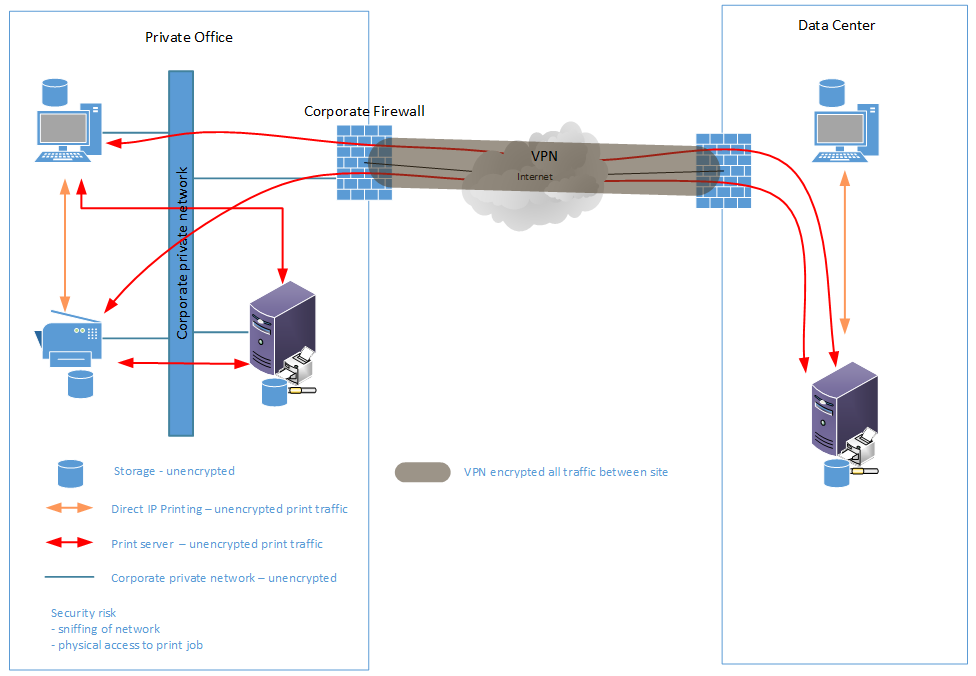
One of the less obvious print security risks is “sniffing” network printer traffic.
A network sniffer can be used to illegally capture confidential data being transmitted on a network. It can be a hardware device or a separate software program that examines traffic on the network and takes snapshot copies of the data.
It is not hard for hackers to “sniff” the data being sent back and forth to the printer given how easy it is to obtain software (from the dark web of course) that literally does it for them.
To prevent users on the network from sniffing print jobs as they go to the printer, find out if printers or print servers support encrypted connections to and from the workstations on the network.
The diagram below shows you what areas on a network are vulnerable to hackers sniffing the network and discovering sensitive data.
A great way to mitigate this problem is by using secure encryption connections when sending print data such as SSL/TLS, IPsec, or other encryption methods.
Printer hacking via the network or internet
Printer hacking through the internet can be extremely destructive.
If a printer, especially older printers or printers without password protection, has the means to connect to the internet they are open to an infinite number of hacks and attacks.
However, password protection alone won’t stop a hacker from attacking a system. Passwords may not always be encrypted when sent between computer and printer, which means someone could easily intercept it.
This gateway means hackers can easily launch a DOS (Denial of Service) attack, upload malware, send malicious documents, or even install ransomware.
To protect against this threat, deploy the proper encryption connections and be sure to keep printer firmware and drivers up-to-date. New updates will often add new or improved security features and patches.
Further Print Security
In general, these print security practices of strategic setup location, password protection, encryption, and up-to-date firmware and drivers are great ways to begin to secure your print environment.
However, even more, security can be achieved through third-party secure print software, which provides enterprises with a complete end-to-end security solution.
In addition to piece of mind about your print workflow security, third-party software often includes additional efficiency, and security tools like print tracking and archiving can also be highly effective in investigating illegal usage of corporate printers and keeping archiving data of who, what, where, and when someone has printed.
Does a Printer Have Memory?
Your printer is just like your other digital devices. It also contains an operating system and hence has a memory. Now printer memory is also of two types. The volatile memory or RAM is lost as soon as you turn off the printer. The non-volatile memory or the hard drive memory is the one that sticks around. Therefore, if you use your printer for secure printing, then you need to take care of non-volatile memory before selling the printer.
Lastly, long-term memory is only in the printers that contain a hard drive. These are usually expensive printers. The low-range or mid-range printers usually do not have the ability to store memory for long.
Check out this free whitepaper on how to achieve secure cloud printing!
Try UniPrint InfinityCloud
Whether you are printing at the office or at home, UniPrint InfinityCloud is the cloud printing solution of choice for your organization.
Recent Posts
- Cloud Printing Management: The Secret to Fewer Help Desk Tickets
- Why Should You Outsource Printing Management? A Comprehensive Overview
- How Cloud Print Management Prevents Print Server Vulnerabilities
- Is Printing Dead?
- How InfinityCloud Outshines Microsoft Universal Print in 2024
- How the Cloud Print Management Software Drives Sustainable Business Practices
- How Cloud Print Management Enhances Your Network Security
- How to Enhance Remote Work Experience with Secure Serverless Printing
- Update to Google Drive Cloud Storage
- A Guide to Preventing Phishing Attacks
- See All